Have you ever got irritated when checking a SPAM email that ended up in your email INBOX instead of SPAM folder?
Imagine the reputation of your business, if someone spoofed your email and sending SPAM content using your email address.
Here is how you can help reduce it.
If you are the domain owner, we can help the email provider to differentiate a legit email from the spoofed ones.
There is a mechanism has been introduce to fight this.
Participating email provider will give feedback upon detecting a spoofed email using your email address/domain.
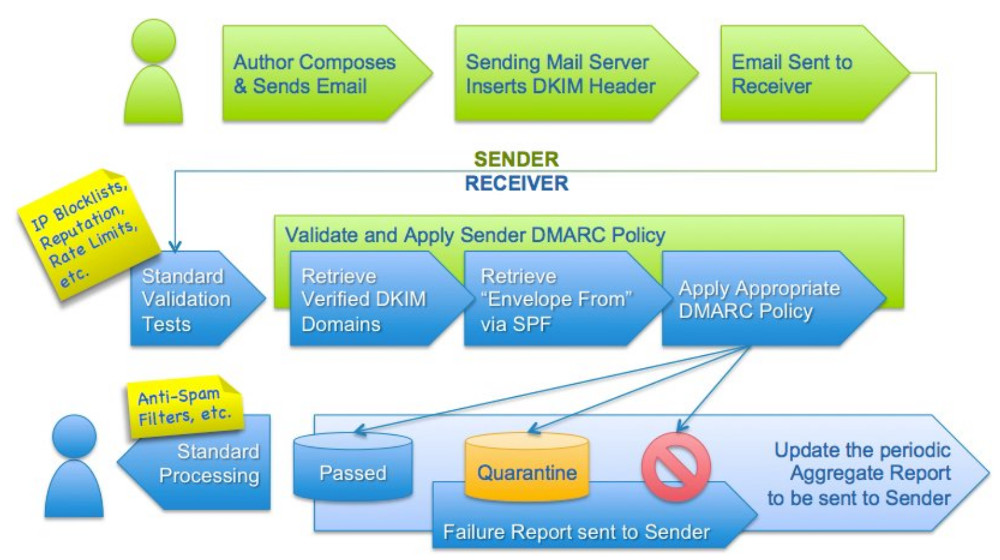
DMARC is a Domain-based Message Authentication, Reporting and Conformance which is an email authentication protocol designed to detect and prevent email spoofing, to improve and monitor protection of the domain from fraudulent email.
A DMARC policy allows a sender to indicate that their messages are protected by SPF and/or DKIM, and tells a receiver what to do if neither of those authentication methods passes – such as junk or reject the message.
Detail of it can be found at https://dmarc.org/
A brief flow is as below:
Here is how to set it up.
Firstly, you have to ensure your email sending server is added to allowed outgoing mailserver listing in SPF record.
Sender Policy Framework (SPF) is a simple email-validation system designed to detect email spoofing by providing a mechanism to allow receiving mail exchangers to check that incoming mail from a domain comes from a host authorized by that domain's administrators.
Secondly, put up DKIM record into DNS server and let your email server sign all the outgoing email.
If you’re using Gmail/Google App for business. This can be easily done at G Suite -> App > Gmail > Authenticate.
Insert the related DKIM record and values into your DNS server and ensure it is propagated properly.
Then enable this in Gmail for each/every outgoing email.
You can check this by viewing the full headers from received emails.
Thirdly, once comfortable with both to be PASS. (SPF & DKIM).
Setup DMARC record into DNS (TXT) record with following hostname.
_dmarc.domain.com
The example value can be as following.
v=DMARC1; p=reject; rua=mailto:[email protected]; ruf=mailto:[email protected]; pct:100;
Where v is for version, p or sp for action to taken can be (none, quarantine, reject) ,
pct for percentage of email to applied (default 100%) .
rua – for reporting of incident of email .
Tag Name Purpose Sample v Protocol version v=DMARC1 pct Percentage of messages subjected to filtering pct=20 ruf Reporting URI for forensic reports ruf=mailto:[email protected] rua Reporting URI of aggregate reports rua=mailto:[email protected] p Policy for organizational domain p=quarantine sp Policy for subdomains of the OD sp=reject adkim Alignment mode for DKIM adkim=s aspf Alignment mode for SPF aspf=r
It is advisable to gradually increase the action step by step.
After done, you can verify by using tools as below.
https://dmarcian.com/dmarc-inspector/
Example for starting, just set to none which DNS record will be is as below:.
nb-namran:~$ dig _dmarc.namran.net txt ; <<>> DiG 9.8.3-P1 <<>> _dmarc.namran.net txt ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54752 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: ;_dmarc.namran.net. IN TXT ;; ANSWER SECTION: _dmarc.namran.net. 299 IN TXT "v=DMARC1\; p=none\; rua=mailto:[email protected]\; ruf=mailto:[email protected]\; fo=1\;" ;; Query time: 61 msec ;; SERVER: 8.8.8.8#53(8.8.8.8) ;; WHEN: Sun May 7 10:37:49 2017 ;; MSG SIZE rcvd: 143
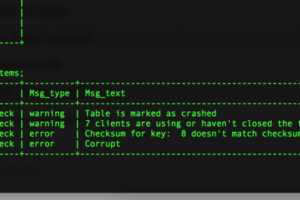
Each time email received by Email service provider, you will receive email in XML format such as below.
google.com [email protected] https://support.google.com/a/answer/2466580 4928472378922823973 1493942400 1494028799 namran.net r r nonenone 100 |
2607:f8b0:4002:c09::22a 1 none pass pass namran.net namran.net pass namran.net pass
Unfortunately, not all email provider with send this report.
Oh, the human readable detail of above XML is as below:
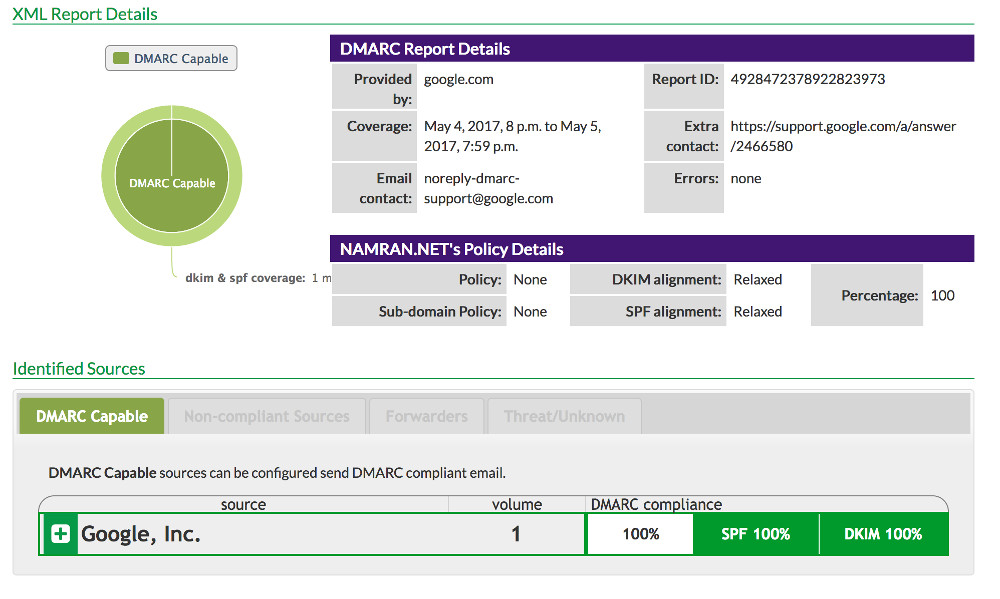
Collectively if everyone is implementing this, it would be better in future.
Here is the result upon receiving a legit email into the recipient INBOX.

Thank you for considering. 🙂